Last Updated on 02/06/2021 by Khushi
The founder Troy Hunt also made a formal public statement that the platform will receive the exposed passwords the FBI finds in its investigations.
Have I Been Pwned (HIBP), this free website used by millions of people to check whether all their credentials have been exposed, has open sourced its code base, announced by founder Troy Hunt today.Troy Hunt at first mentioned the plans to open source the HIBP code base last summer. Now, as the requests for the website’s Pwned Passwords approached 1 billion per month, he has confirmed that it is officially open source through the .NET Foundation, an independent 501(c) non-profit organization.

Image courtesy : troyhunt.com
Hunt explained in a blog post that there are a few reasons Pwned Passwords works well for the open source model, which is why he decided to start there.Image courtesy : troyhunt.comFor beginners, Pwned Passwords has a simple code base containing Azure Storage, a single Azure Function, and a Cloudflare worker. It also consists of its own domain, Cloudflare account, and Azure services, so that it can be picked up and open sourced under one’s own steam of the rest of HIBP.
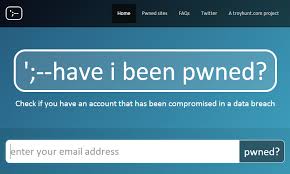
Image courtesy : troyhunt.com
He further added, it is non-commercial with no API costs or enterprise services, like the other parts of HIBP. And finally, the data driving Pwned Passwords is already free of cost available in the public domain through the easily downloadable hash sets.Image courtesy : troyhunt.com Hunt wrote, I can conventionally ‘lift and shift’ Pwned Passwords into an open source land in a very straightforward fashion which makes it the most obvious place to get started. He added, It is also good timing, because it is now a part of many of the online services, and this makes it certain that anybody can run their own Pwned Passwords instance if they wanted to.
He hopes that this will encourage getting adopted to the service.Troy Hunt also made it clear to the public today that HIBP will receive compromised passwords which are discovered as part of investigations by the FBI. This website will provide officials directions to feed the passwords into HIBP and surface them through the Pwned Passwords tool, he further explained. These identified passwords will be made available in SHA-1 and NTLM hash pairs, which aligns with Pwned Password’s current storage constructs, noting he doesn’t need them in plaintext, he added.










