Last Updated on 27/01/2022 by Nidhi Khandelwal
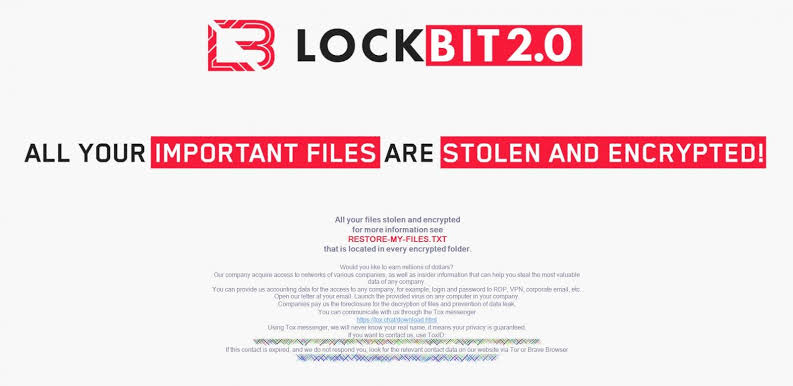
LockBit is the newest ransomware group whose Linux encryption has been revealed to target VMware ESXi virtual machines for encryption.
Virtual machines are becoming more popular in the industry as a way to save computer resources, consolidate servers, and simplify backups.
As a result, ransomware gangs have modified their tactics in the last year to produce Linux encryptors that target the popular VMware vSphere and ESXi virtualization platforms.
While ESXi is not literally a Linux distribution, it does share many of its properties, such as the ability to run ELF64 Linux executables.
Lockbit is a malware that attacks VMware ESXi systems.
On the RAMP hacking forums in October, LockBit started promoting the new features of its Ransomware-as-a-Service operation, including a new Linux encryption that targets VMware ESXi virtual machines.
Trend Micro researchers looked at the ransomware gang’s Linux encryption and outlined how it’s used to attack VMWare ESXi and vCenter systems in a new paper.
Similar encryptors have been reported in the past by HelloKitty, BlackMatter, REvil, AvosLocker, and the Hive ransomware operations, according to BleepingComputer.
LockBits, like other Linux encryptors, has a command-line interface that allows users to customize their assaults by enabling and disabling certain features.
As illustrated in the image below, these features include the ability to define how large a file and how many bytes to encrypt, as well as whether to halt operating virtual machines or delete free space afterward.










