Last Updated on 29/07/2020 by TheDigitalHacker
Maze ransomware operators have claimed that they were successfully able to breach the LG electronics database. For this, they also released a zip file of 3.6 GB memory space. It is labeled as 1% LG electronics. The data is though now password protected, which the operators.
This leak could be seen as a warning message for the company to abide by the terms of maze ransomware.
As part of Cyble’s regular dark web monitoring, it’s researchers came across the data leak of LG Electronics been published by the Maze ransomware operators. This incident took place just after the WorldNet Telecommunications hack now the LG electronics fell as a victim of the Maze ransomware operators.
LG ELECTRONICS
LG is a South Korean company and one of the big names in the electronics market. LG is a combination of four business units: Home Entertainment, Mobile Communications, Home Appliances & Air Solutions, and Vehicle Components. Currently, the company has ongoing 128 operations worldwide and employing 83,000 significant workforces.
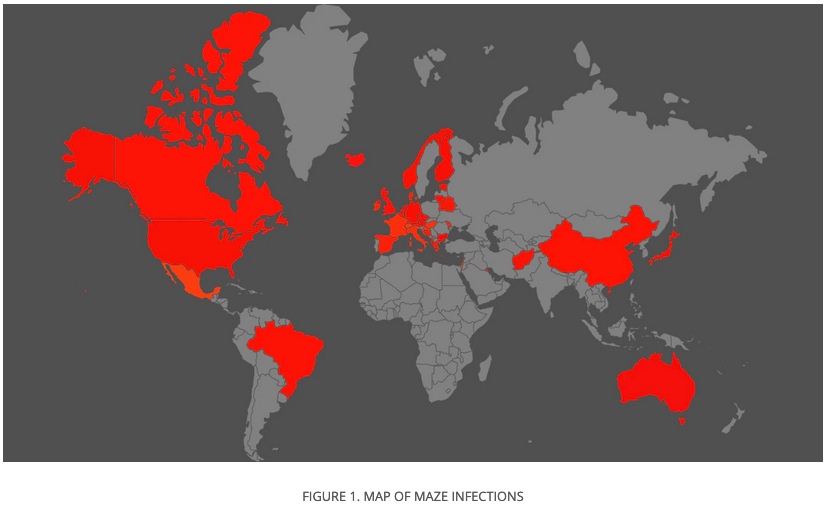
Maze infections Telemetry map till 1st quarter 2020
The hack
Three days back, the maze ransomware in a press release warned the companies not to try to recover information themselves because firstly, they state that the maze locker can’t be decrypted without the assistance of anyone from the maze team. Also, secondly, companies would then be charged double or even four times the money, and while still being in the same situation.
Lastly, in the press release, they mentioned about data leak of LG Electronics to take place soon, which has occurred now.
As per the verification, the reporter found information about the issue and three screenshots that have been shared as a part of the proof of the data breach. One of the screenshots seems to have the software updates of their operating systems used in various machines. LG must take some step else many such information will soon be coming in the coming days.
Do you know about a bug/data breach/vulnerability that you want to report anonymously?
Submit this simple form at Data Breach/Vulnerability/Hack TheDIgitalHacker










